Microsoft SC-200 Real Exam Questions
The questions for SC-200 were last updated at Mar 06,2025.
- Exam Code: SC-200
- Exam Name: Microsoft Security Operations Analyst
- Certification Provider: Microsoft
- Latest update: Mar 06,2025
Which rule setting should you configure to meet the Microsoft Sentinel requirements?
- A . From Set rule logic, turn off suppression.
- B . From Analytic rule details, configure the tactics.
- C . From Set rule logic, map the entities.
- D . From Analytic rule details, configure the severity.
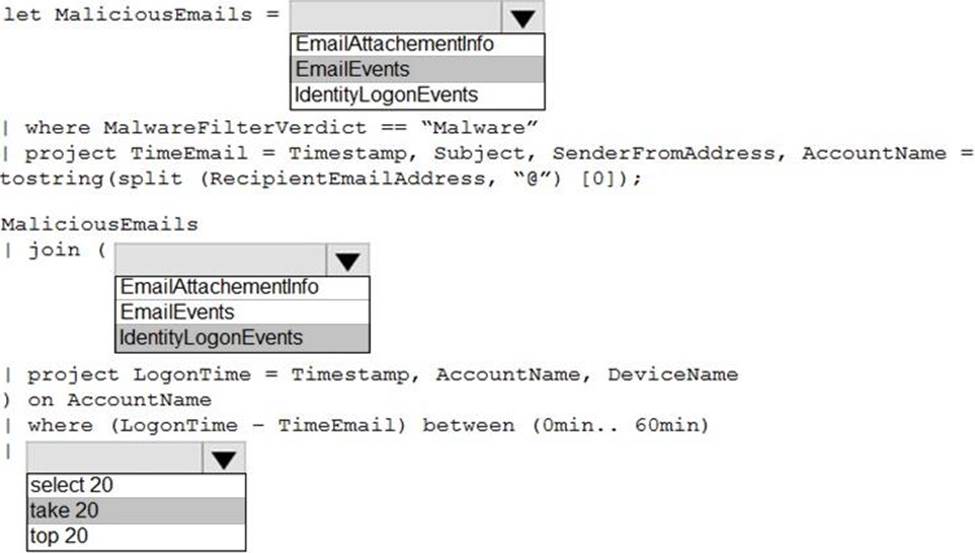
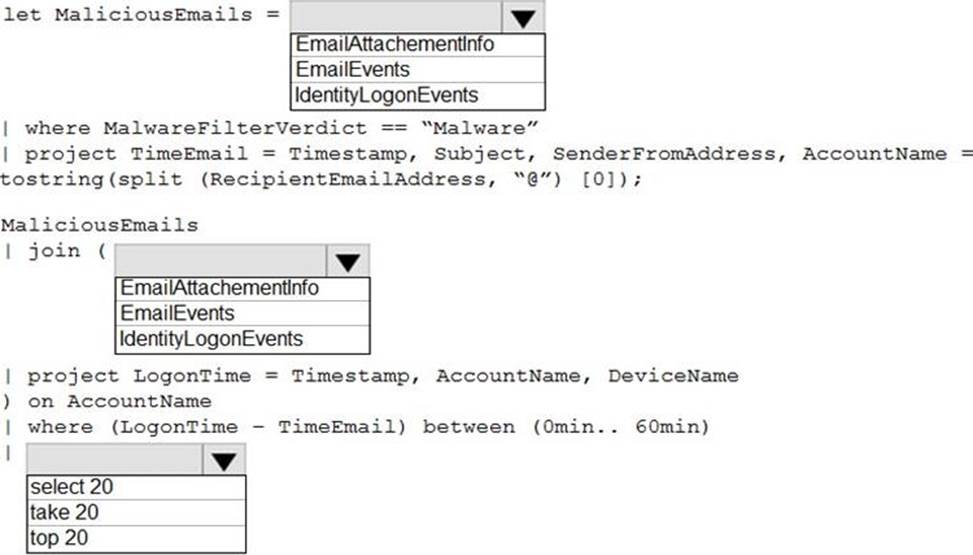
HOTSPOT
You are informed of an increase in malicious email being received by users.
You need to create an advanced hunting query in Microsoft 365 Defender to identify whether the accounts of the email recipients were compromised. The query must return the most recent 20 sign-ins performed by the recipients within an hour of receiving the known malicious email.
How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Topic 4, Misc. Questions
Fabrikam. Inc. is a financial services company.
The company has branch offices in New York. London, and Singapore. Fabrikam has remote users located across the globe. The remote users access company resources, including cloud resources, by using a VPN connection to a branch office.
The network contains an Active Directory Domain Services (AD DS) forest named fabrikam.com that syncs with an Azure AD tenant named fabrikam.com. To sync the forest, Fabrikam uses Azure AD Connect with pass-through authentication enabled and password hash synchronization disabled. The fabrikam.com forest contains two global groups named Group1 and Group2.
All the users at Fabrikam are assigned a Microsoft 365 E5 license and an Azure Active Directory Premium Plan 2 license. Fabrikam implements Microsoft Defender for Identity and Microsoft Defender for Cloud Apps and enables log collectors.
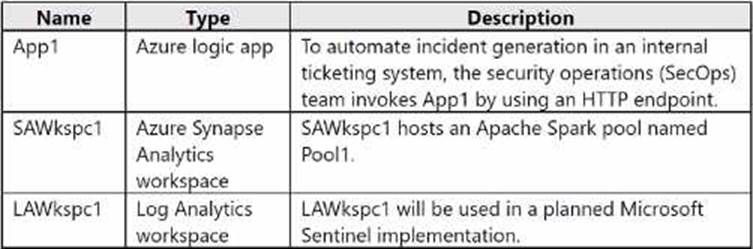
Fabrikam has an Azure subscription that contains the resources shown in the following table.
Fabrikam has an Amazon Web Services (AWS) account named Account1. Account1 contains 100 Amazon Elastic Compute Cloud (EC2) instances that run a custom Windows Server 2022. The image includes Microsoft SQL Server 2019 and does NOT have any agents installed.
When the users use the VPN connections. Microsoft 365 Defender raises a high volume of impossible travel alerts that are false positives. Defender for Identity raises a high volume of Suspected DCSync attack alerts that are false positives.
Fabrikam plans to implement the following services:
• Microsoft Defender for Cloud
• Microsoft Sentinel
Fabrikam identifies the following business requirements:
• Use the principle of least privilege, whenever possible.
• Minimize administrative effort.
Fabrikam identifies the following Microsoft Defender for Cloud Apps requirements:
• Ensure that impossible travel alert policies are based on the previous activities of each user.
• Reduce the amount of impossible travel alerts that are false positives.
Minimize the administrative effort required to investigate the false positive alerts.
Fabrikam identifies the following Microsoft Defender for Cloud requirements:
• Ensure that the members of Group2 can modify security policies.
• Ensure that the members of Group1 can assign regulatory compliance policy initiatives at the Azure subscription level.
• Automate the deployment of the Azure Connected Machine agent for Azure Arc-enabled servers to the existing and future resources of Account1.
• Minimize the administrative effort required to investigate the false positive alerts.
Fabrikam identifies the following Microsoft Sentinel requirements:
• Query for NXDOMAIN DNS requests from the last seven days by using built-in Advanced Security Information Model (ASIM) unifying parsers.
• From AWS EC2 instances, collect Windows Security event log entries that include local group membership changes.
• Identify anomalous activities of Azure AD users by using User and Entity Behavior Analytics (UEBA).
• Evaluate the potential impact of compromised Azure AD user credentials by using UEBA.
• Ensure that App1 is available for use in Microsoft Sentinel automation rules.
• Identify the mean time to triage for incidents generated during the last 30 days.
• Identify the mean time to close incidents generated during the last 30 days.
• Ensure that the members of Group1 can create and run playbooks.
• Ensure that the members of Group1 can manage analytics rules.
• Run hunting queries on Pool! by using Jupyter notebooks.
• Ensure that the members of Group2 can manage incidents.
• Maximize the performance of data queries.
• Minimize the amount of collected data.
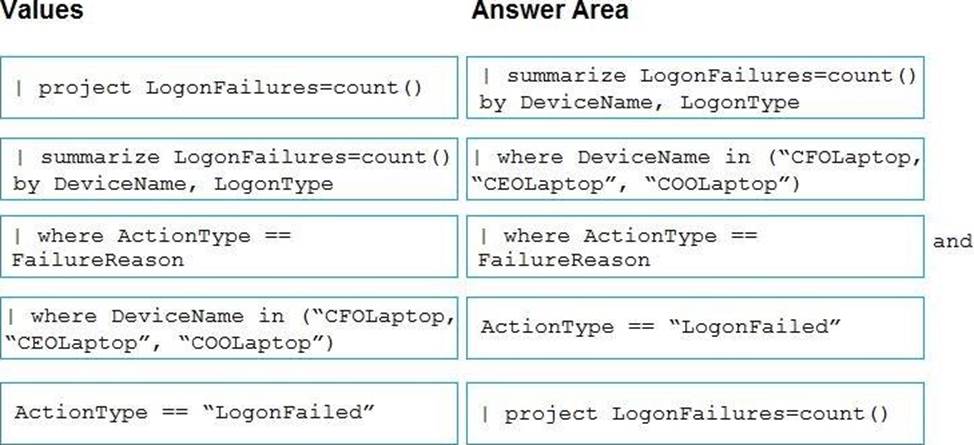
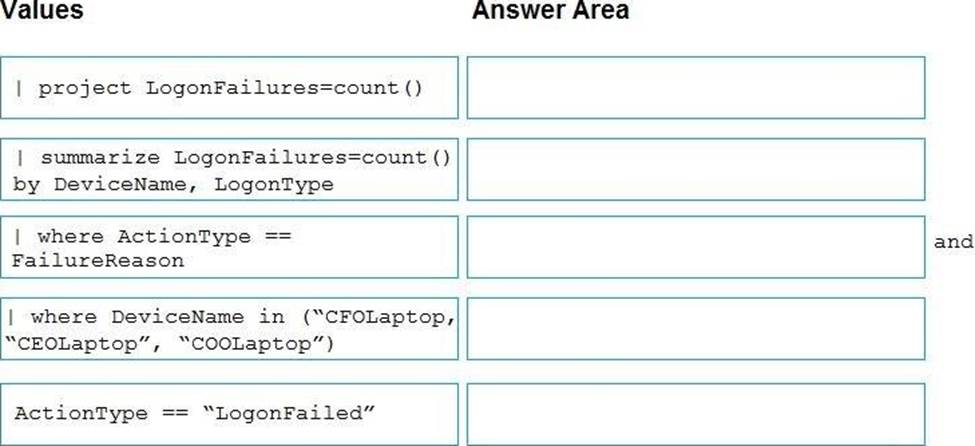
DRAG DROP
You are investigating an incident by using Microsoft 365 Defender.
You need to create an advanced hunting query to detect failed sign-in authentications on three devices named CFOLaptop, CEOLaptop, and COOLaptop.
How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You use Azure Security Center.
You receive a security alert in Security Center.
You need to view recommendations to resolve the alert in Security Center.
Solution: From Security alerts, you select the alert, select Take Action, and then expand the Prevent future attacks section.
Does this meet the goal?
- A . Yes
- B . No
You need to receive a security alert when a user attempts to sign in from a location that was never used by the other users in your organization to sign in.
Which anomaly detection policy should you use?
- A . Impossible travel
- B . Activity from anonymous IP addresses
- C . Activity from infrequent country
- D . Malware detection
You need to implement the Defender for Cloud requirements.
Which subscription-level role should you assign to Group1?
- A . Security Admin
- B . Owner
- C . Security Assessment Contributor
- D . Contributor
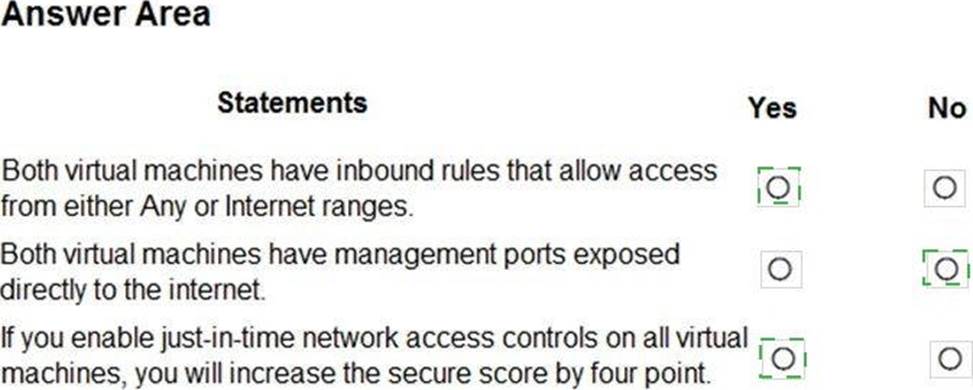
HOTSPOT
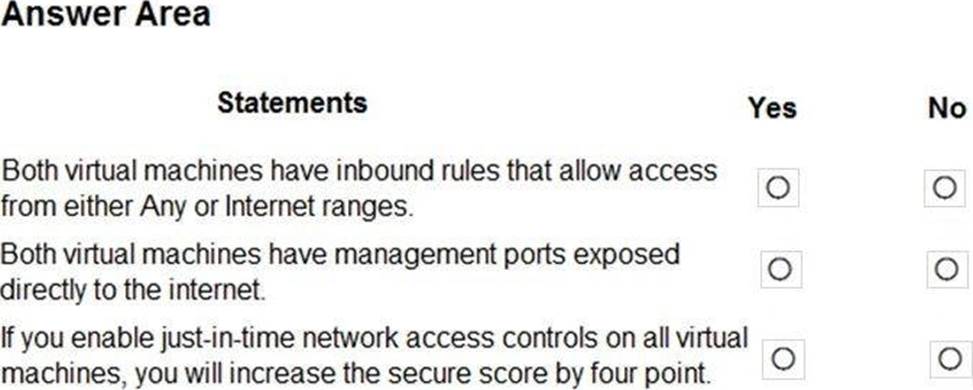
You manage the security posture of an Azure subscription that contains two virtual machines name vm1 and vm2.
The secure score in Azure Security Center is shown in the Security Center exhibit. (Click the Security Center tab.)
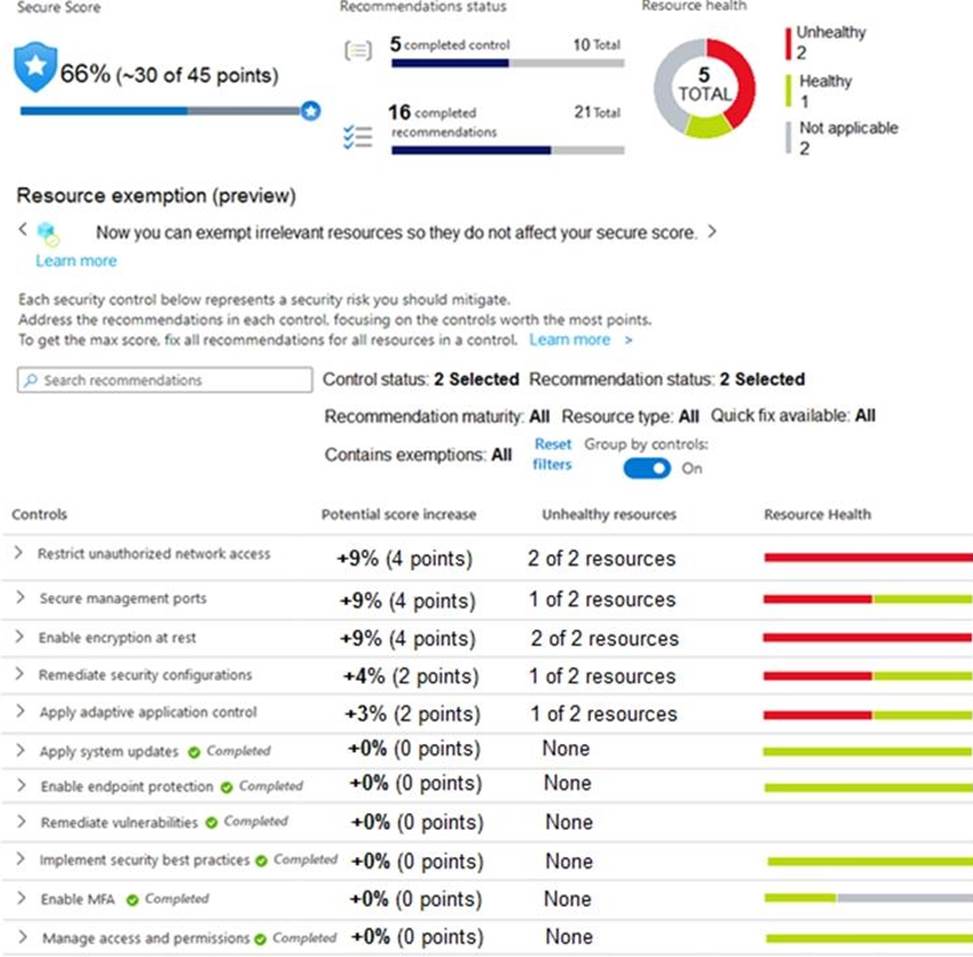
Azure Policy assignments are configured as shown in the Policies exhibit. (Click the Policies tab.)
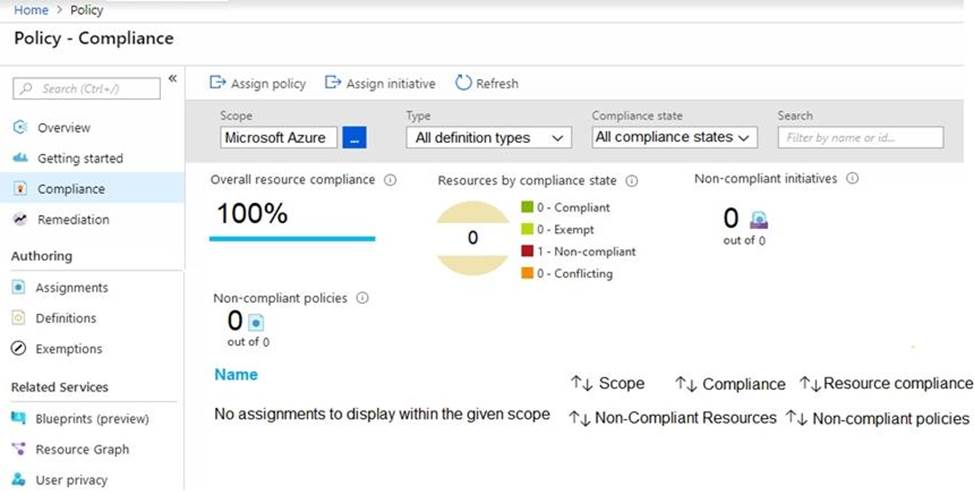
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Topic 3, Adatum Corporation
Overview
Adatum Corporation is a United States-based financial services company that has regional offices in New York, Chicago, and San Francisco.
The on-premises network contains an Active Directory Domain Services (AD DS) forest named corp.adatum.com that syncs with an Azure AD tenant named adatum.com. All user and group management tasks are performed in corp.adatum.com. The corp.adatum.com domain contains a group named Group! that syncs with adatum.com.
All the users at Adatum are assigned a Microsoft 365 E5 license and an Azure Active Directory Perineum 92 license.
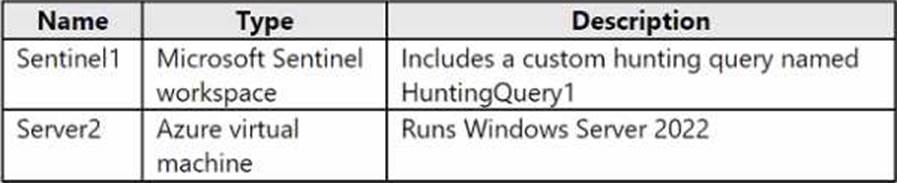
The cloud environment contains a Microsoft 365 subscription, an Azure subscription linked to the adatum.com tenant, and the resources shown in the following table.
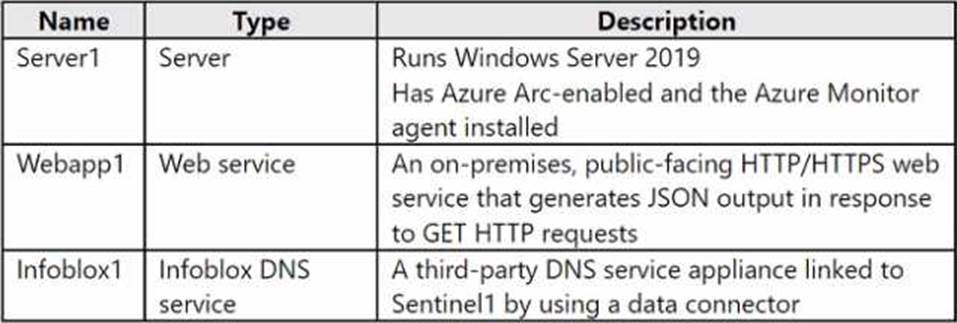
The on-premises network contains the resources shown in the following table.
Adatum plans to perform the following changes;
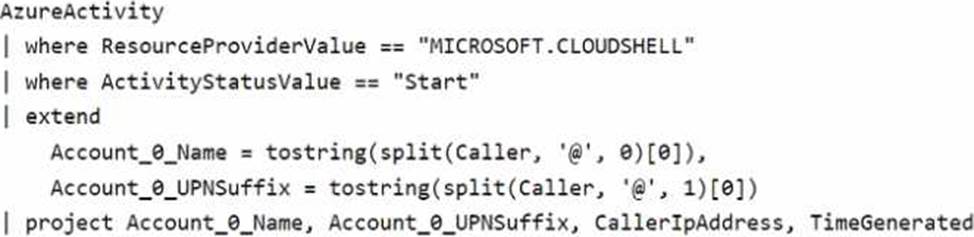
• Implement a query named rulequery1 that will include the following KQL query.
• Implement a Microsoft Sentinel scheduled rule that generates incidents based on rulequery1. Adatum identifies the following Microsoft Defender for Cloud requirements:
• The members of Group1 must be able to enable Defender for Cloud plans and apply regulatory compliance initiatives.
• Microsoft Defender for Servers Plan 2 must be enabled on all the Azure virtual machines.
• Server2 must be excluded from agentless scanning.
Adatum identifies the following Microsoft Sentinel requirements:
• Implement an Advanced Security Information Model (ASIM) query that will return a count of DNS requests that results in an NXDOMAIN response from Infoblox1.
• Ensure that multiple alerts generated by rulequery1 in response to a single user launching Azure Cloud Shell multiple times are consolidated as a single incident.
• Implement the Windows Security Events via AMA connector for Microsoft Sentinel and configure it to monitor the Security event log of Server1.
• Ensure that incidents generated by rulequery1 are closed automatically if Azure Cloud Shell is launched by the company’s SecOps team.
• Implement a custom Microsoft Sentinel workbook named Workbook1 that will include a query to dynamically retrieve data from Webapp1.
• Implement a Microsoft Sentinel near-real-time (NRT) analytics rule that detects sign-ins to a designated break glass account
• Ensure that HuntingQuery1 runs automatically when the Hunting page of Microsoft Sentinel in the Azure portal is accessed.
• Ensure that higher than normal volumes of password resets for corp.adatum.com user accounts are detected.
• Minimize the overhead associated with queries that use ASIM parsers.
• Ensure that the Group1 members can create and edit playbooks.
• Use built-in ASIM parsers whenever possible.
Adatum identifies the following business requirements:
• Follow the principle of least privilege whenever possible.
• Minimize administrative effort whenever possible. Directory Perineum 92 license.
You need to configure event monitoring for Server1. The solution must meet the Microsoft Sentinel requirements.
What should you create first?
- A . a Microsoft Sentinel automation rule
- B . a Microsoft Sentinel scheduled query rule
- C . a Data Collection Rule (DCR)
- D . an Azure Event Grid topic
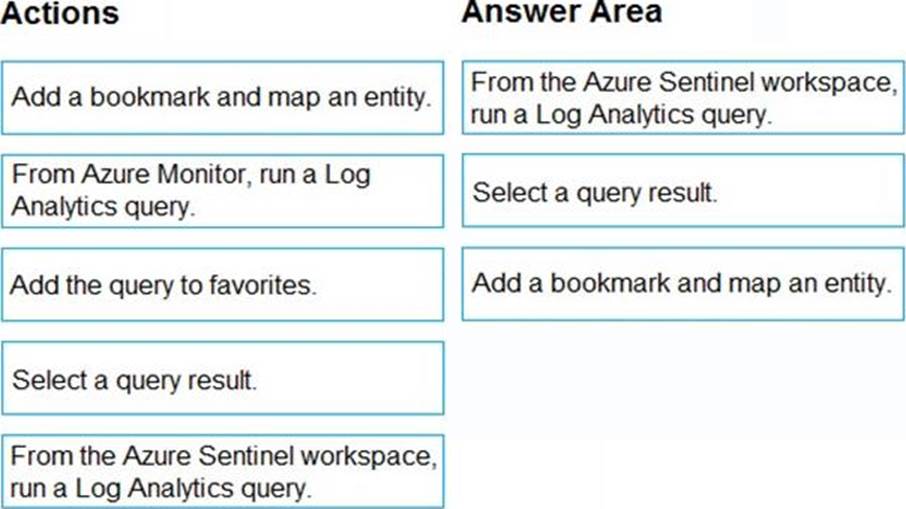
DRAG DROP
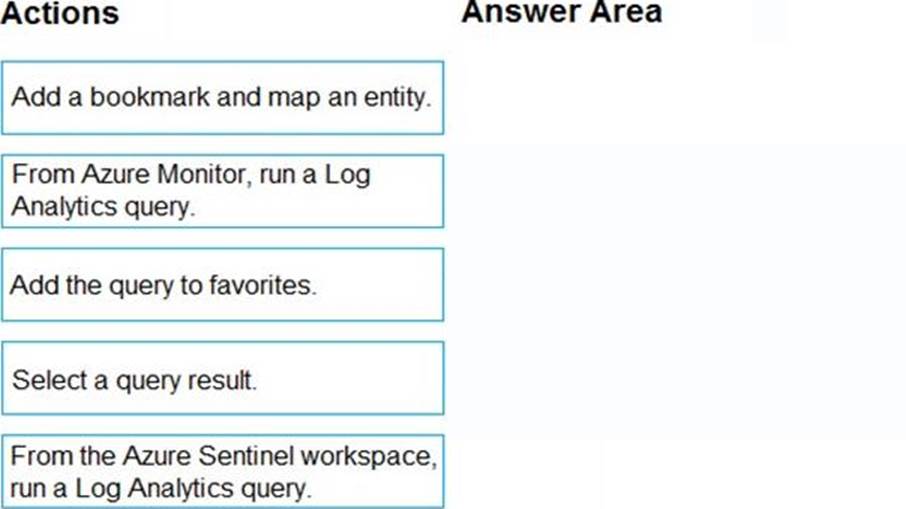
You need to add notes to the events to meet the Azure Sentinel requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of action to the answer area and arrange them in the correct order.
You plan to create a custom Azure Sentinel query that will provide a visual representation of the security alerts generated by Azure Security Center.
You need to create a query that will be used to display a bar graph.
What should you include in the query?
- A . extend
- B . bin
- C . count
- D . workspace