Microsoft AZ-500 Real Exam Questions
The questions for AZ-500 were last updated at Apr 16,2025.
- Exam Code: AZ-500
- Exam Name: Microsoft Azure Security Technologies
- Certification Provider: Microsoft
- Latest update: Apr 16,2025
HOTSPOT
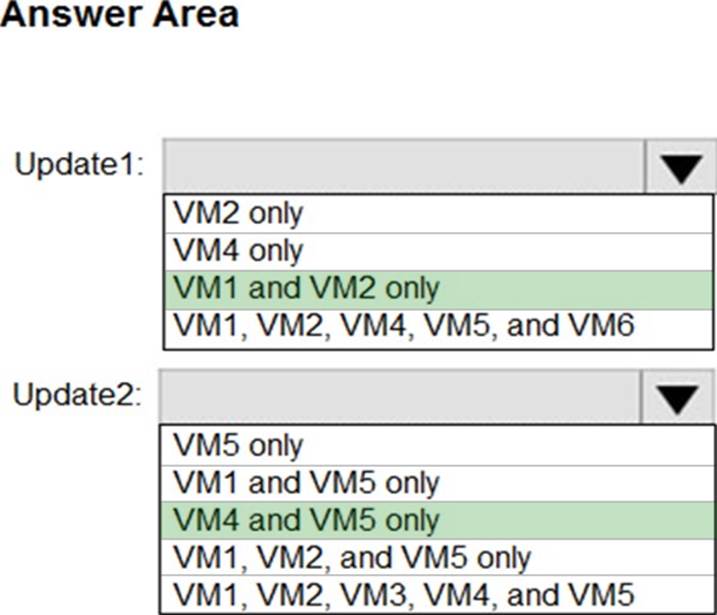
You have Azure virtual machines that have Update Management enabled.
The virtual machines are configured as shown in the following table.
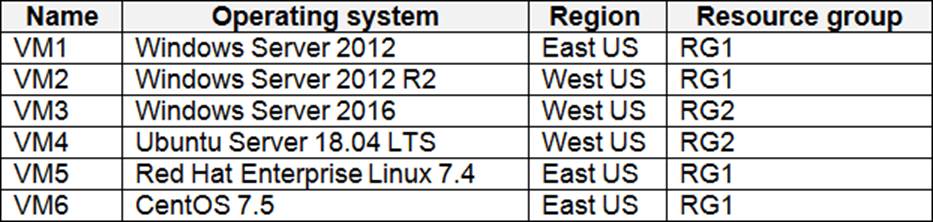
You schedule two update deployments named Update1 and Update2. Update1 updates VM3.
Update2 updates VM6.
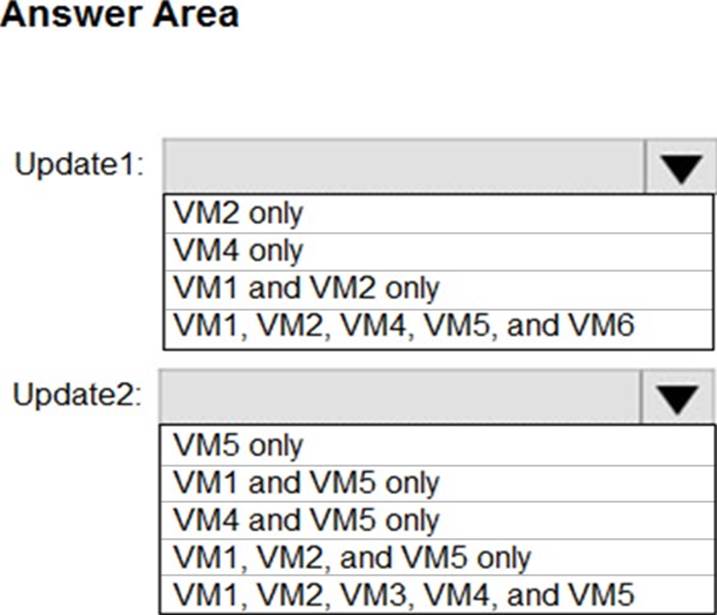
Which additional virtual machines can be updated by using Update1 and Update2? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Topic 1, Litware, inc
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other question on this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next sections of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question on this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.
Overview
Litware, Inc. is a digital media company that has 500 employees in the Chicago area and 20 employees in the San Francisco area.
Existing Environment
Litware has an Azure subscription named Sub1 that has a subscription ID of 43894a43-17c2-4a39-8cfc-3540c2653ef4.
Sub1 is associated to an Azure Active Directory (Azure AD) tenant named litwareinc.com. The tenant contains the user objects and the device objects of all the Litware employees and their devices. Each user is assigned an Azure AD Premium P2 license. Azure AD Privileged Identity Management (PIM) is activated.
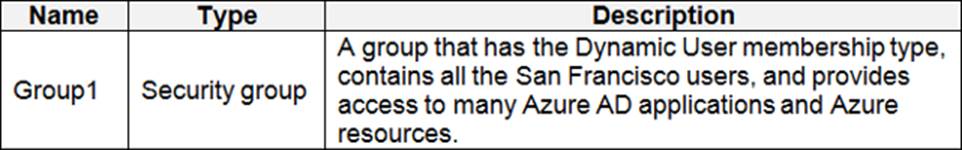
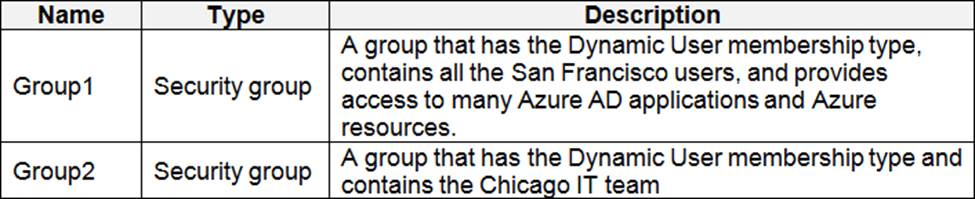
The tenant contains the groups shown in the following table.
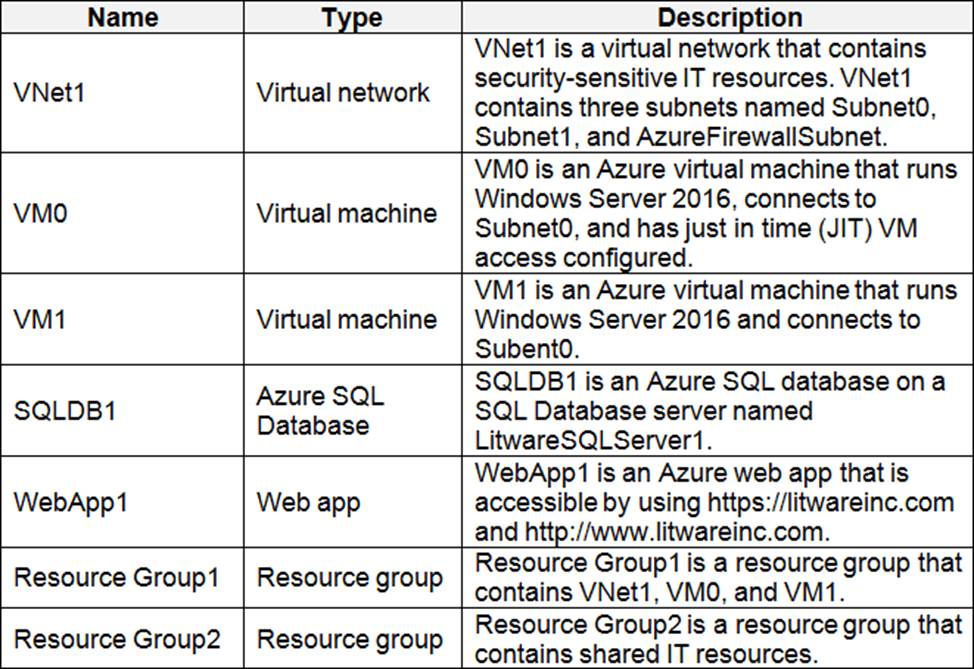
The Azure subscription contains the objects shown in the following table.
Azure Security Center is set to the Free tier.
Planned changes
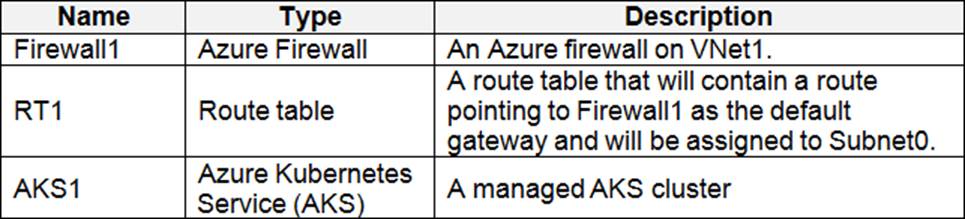
Litware plans to deploy the Azure resources shown in the following table.
Identity and Access Requirements
Litware identifies the following identity and access requirements:
✑ All San Francisco users and their devices must be members of Group1.
✑ The members of Group2 must be assigned the Contributor role to Resource Group2 by using a permanent eligible assignment.
✑ Users must be prevented from registering applications in Azure AD and from consenting to applications that access company information on the users’ behalf.
Platform Protection Requirements
Litware identifies the following platform protection requirements:
✑ Microsoft Antimalware must be installed on the virtual machines in Resource Group1.
✑ The members of Group2 must be assigned the Azure Kubernetes Service Cluster Admin Role.
✑ Azure AD users must be to authenticate to AKS1 by using their Azure AD credentials.
✑ Following the implementation of the planned changes, the IT team must be able to connect to VM0 by using JIT VM access.
✑ A new custom RBAC role named Role1 must be used to delegate the administration of the managed disks in Resource Group1. Role1 must be available only for Resource Group1.
Security Operations Requirements
Litware must be able to customize the operating system security configurations in Azure Security Center.
You need to meet the identity and access requirements for Group1.
What should you do?
- A . Add a membership rule to Group1.
- B . Delete Group1. Create a new group named Group1 that has a membership type of Office 365. Add users and devices to the group.
- C . Modify the membership rule of Group1.
- D . Change the membership type of Group1 to Assigned. Create two groups that have dynamic memberships. Add the new groups to Group1.
Topic 4, Mix Questions
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these
questions will not appear in the review screen.
You have an Azure Subscription named Sub1.
You have an Azure Storage account named Sa1 in a resource group named RG1.
Users and applications access the blob service and the file service in Sa1 by using several shared access
signatures (SASs) and stored access policies.
You discover that unauthorized users accessed both the file service and the blob service.
You need to revoke all access to Sa1.
Solution: You generate new SASs.
Does this meet the goal?
- A . Yes
- B . No
Topic 4, Mix Questions
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these
questions will not appear in the review screen.
You have an Azure Subscription named Sub1.
You have an Azure Storage account named Sa1 in a resource group named RG1.
Users and applications access the blob service and the file service in Sa1 by using several shared access
signatures (SASs) and stored access policies.
You discover that unauthorized users accessed both the file service and the blob service.
You need to revoke all access to Sa1.
Solution: You generate new SASs.
Does this meet the goal?
- A . Yes
- B . No
You have an Azure subscription named Sub1 that contains the Azure key vaults shown in the following table.
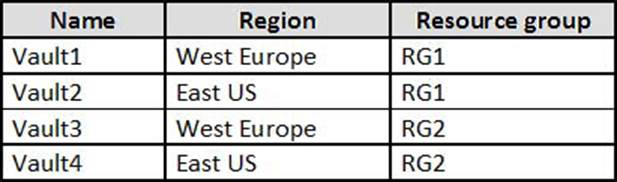
In Sub1, you create a virtual machine that has the following configurations:
• Name:VM1
• Size: DS2v2
• Resource group: RG1
• Region: West Europe
• Operating system: Windows Server 2016
You plan to enable Azure Disk Encryption on VM1.
In which key vaults can you store the encryption key for VM1?
- A . Vault1 or Vault3 only
- B . Vault1, Vault2, Vault3, or Vault4
- C . Vault1 only
- D . Vault1 or Vault2 only
You have an Azure subscription named Sub1 that is associated to an Azure Active Directory (Azure AD) tenant named contoso.com.
You are assigned the Global administrator role for the tenant. You are responsible for managing Azure Security Center settings.
You need to create a custom sensitivity label.
What should you do first?
- A . Create a custom sensitive information type.
- B . Elevate access for global administrators in Azure AD.
- C . Upgrade the pricing tier of the Security Center to Standard.
- D . Enable integration with Microsoft Cloud App Security.
Your network contains an Active Directory forest named contoso.com. You have an Azure Directory (Azure AD) tenant named contoso.com.
You plan to configure synchronization by using the Express Settings installation option in Azure AD Connect.
You need to identify which roles and groups are required to perform the planned configurations. The solution must use the principle of least privilege.
Which two roles and groups should you identify? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . the Domain Admins group in Active Directory
- B . the Security administrator role in Azure AD
- C . the Global administrator role in Azure AD
- D . the User administrator role in Azure AD
- E . the Enterprise Admins group in Active Directory
Your network contains an Active Directory forest named contoso.com. You have an Azure Directory (Azure AD) tenant named contoso.com.
You plan to configure synchronization by using the Express Settings installation option in Azure AD Connect.
You need to identify which roles and groups are required to perform the planned configurations. The solution must use the principle of least privilege.
Which two roles and groups should you identify? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
- A . the Domain Admins group in Active Directory
- B . the Security administrator role in Azure AD
- C . the Global administrator role in Azure AD
- D . the User administrator role in Azure AD
- E . the Enterprise Admins group in Active Directory
HOTSPOT
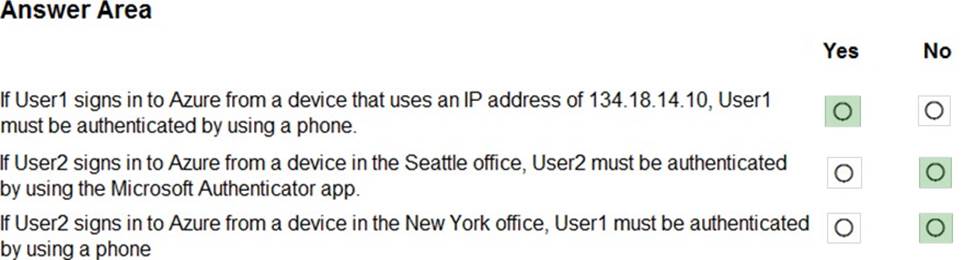
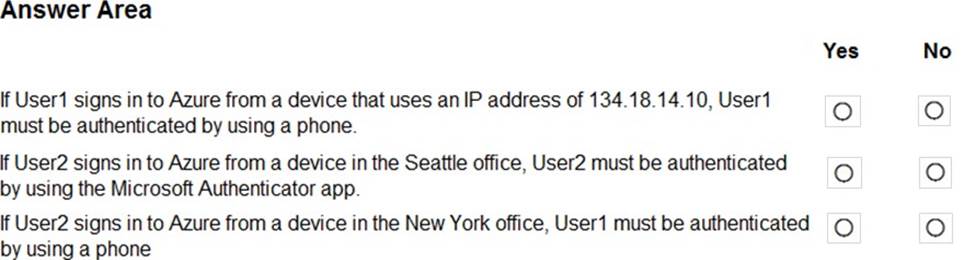
Your company has two offices in Seattle and New York. Each office connects to the Internet by using a NAT device.
The offices use the IP addresses shown in the following table.
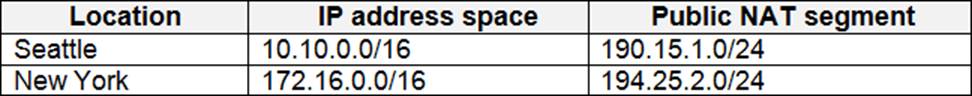
The company has an Azure Active Directory (Azure AD) tenant named contoso.com.
The tenant contains the users shown in the following table.
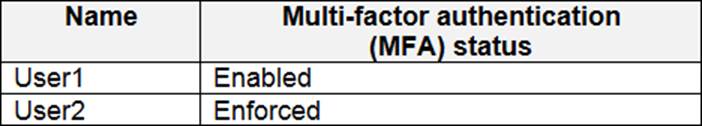
The MFA service settings are configured as shown in the exhibit. (Click the Exhibit tab.)
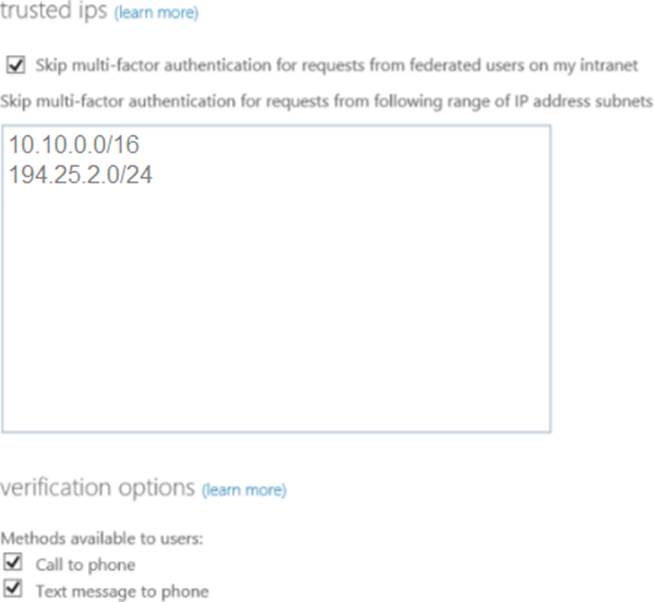
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Your network contains an on-premises Active Directory domain named corp.contoso.com.
You have an Azure subscription named Sub1 that is associated to an Azure Active Directory (Azure AD) tenant named contoso.com.
You sync all on-premises identities to Azure AD.
You need to prevent users who have a givenName attribute that starts with TEST from being synced to Azure AD. The solution must minimize administrative effort.
What should you use?
- A . Synchronization Rules Editor
- B . Web Service Configuration Tool
- C . the Azure AD Connect wizard
- D . Active Directory Users and Computers